We secure embedded systems
IP Cores and Products
ASIC/SoC Security Services
Consulting & hardware software co-design services for secure ASIC or SoC systems.
FPGA Security Services
Consulting & hardware software co-design services for secure FPGA based embedded systems.
Embedded Security Services
IEC 62443-4-2 Engineering Assessment
Manufacturers of embedded and industrial devices are increasingly facing new cybersecurity requirements that impact product development and architecture decisions.
You might encounter situations such as:
- A customer requires IEC 62443 certification for your product
- You want to prepare your product architecture for upcoming regulations such as the Cyber Resilience Act (CRA)
- Your security architecture has evolved over time and you want to evaluate whether the existing security mechanisms are implemented effectively.
Our technical product evaluation helps you assess your product against the IEC 62443-4-2 component security requirements and identify what changes are needed to reach your target Security Level (SL).
IP Core Evaluation Portal
The KiviCore IP Core Evaluation Portal is a platform where registered users can access IP Core evaluation packages for various FPGA platforms for free.
After registration you can:
- Download IP Core evaluation packages for supported FPGAs
- Access detailed documentation and datasheets
- Receive updates about new IP Cores and features
- Get web support for downloaded IP Core packages
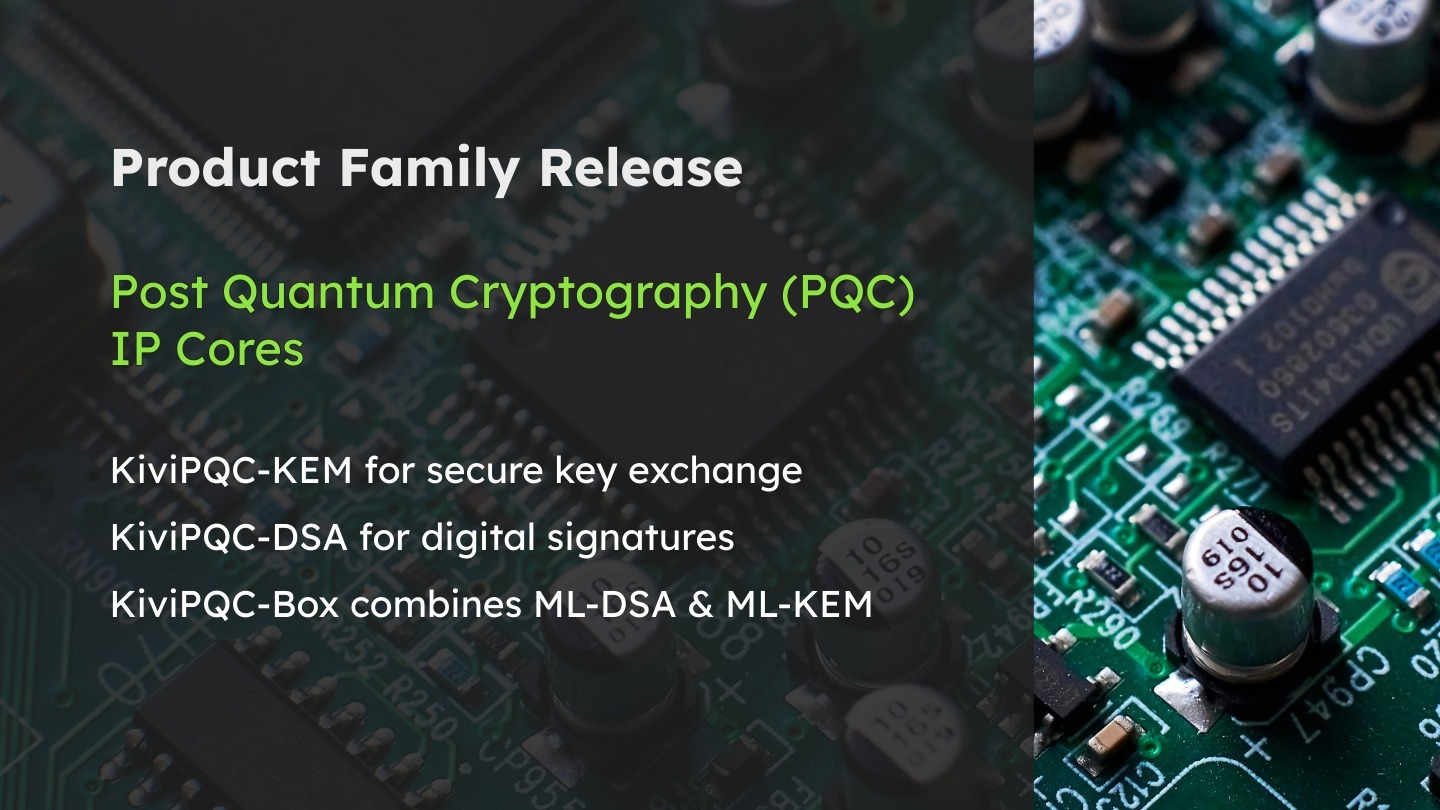
Post Quantum Cryptography (PQC) IP Core Family
Post-quantum cryptography IP cores designed for secure FPGA and ASIC implementations. The PQC familiy includes KiviPQC-KEM (ML-KEM, FIPS 203) for key exchange, KiviPQC-DSA (ML-DSA, FIPS 204) for digital signatures, and KiviPQC-Box, which integrates both algorithms. Each is optimized for minimal logic usage, easy AXI4-Lite and HAL/API integration, and available in Fast and Tiny versions.
Security Product Check-Up
Our Security Product Check-Up provides a fast, comprehensive assessment to help you launch your embedded product with confidence. Within two weeks, we identify the real security risks affecting your system and outline the most important measures to address them. Instead of lengthy processes and complex reports, you receive clear guidance and practical recommendations.

Cyber Resilience Act
The Cyber Resilience Act (CRA) places significant pressure on manufacturers and developers of embedded systems. Companies will need to undergo regular assessments to verify that their products meet the required cybersecurity standards.
We help companies to adapt their embedded products to be compliant with the CRA and to evaluate and implement suitable security measures.