Embedded Electronics
Consulting & Design Services
How we can help
Services for secure embedded Electronics
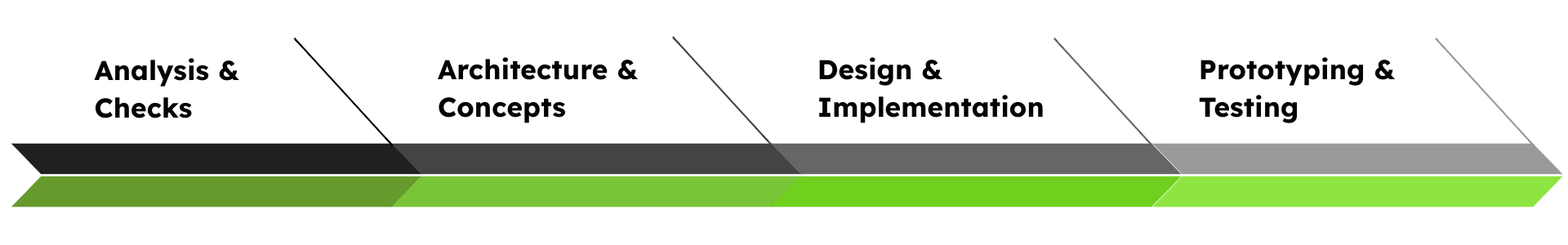
1
Analysis & Check
- Risk assessment
- Definition of security goals and requirements
- Analysis of existing embedded system security concepts & features
- Compliance check & gap analysis of embedded systems in relation to cybersecurity standards (e.g. Cyber Reslience Act)
2
Architecture & Concepts
- Development of secure concepts & architectures
- Optimization of existing security concepts
3
Design & Implementation
- Analysis and evaluation of different software implementation approaches
- Integration of security mechanisms
- Secure boot
- Secure life cycle
- Secure key exchange
- Secure communication
- Secure updates
- Secure storage
4
Prototyping & Testing
- Development of PoCs for security solutions
- Design and evaluation of embedded hardware & software demonstrators
- Carrying out threat analyses and simulation-based security tests
- Verifying security-critical designs to ensure protection against side-channel attacks and other vulnerabilities
Our embedded Security Consulting & Design Offerings

Cyber Resilience Act
Due to the Cyber Reslience Act manufacturers of microelectronics must take action. Manufacturers must assess which attacks and exploits, regardless of an attacker’s motives, could affect the device.
We offer services to help you with that.

MACSec and Key Agreement
MACsec stands for Media Access Control Security and is a standard to secure point-to-point network communication on the data data link layer (Layer 2) of the OSI 7 layer model.
We offer the development & implementation of MACsec concepts based on MKA and pre-shared keys.

IPSec & Key Agreement
IPsec is a Layer 3 encryption technology to secure IP traffic. To utilize this IPsec, an Internet Key Exchange protocol IKEv2 is needed. IKEv2 creates secure associations, negotiates encryption, and generates session keys.
We can help you by creating IPsec and IKE concepts and implementing them onto different target platforms.

Bluetooth Low Energy Security
Bluetooth Low Energy is widely used in many embedded systems to wirelessly connect to other devices. Security measures such as secure pairing, secure authentication, or data encryption will become more important.
We support many different BLE hardware and software stacks such as Espressif, Nordic or Zephyr.